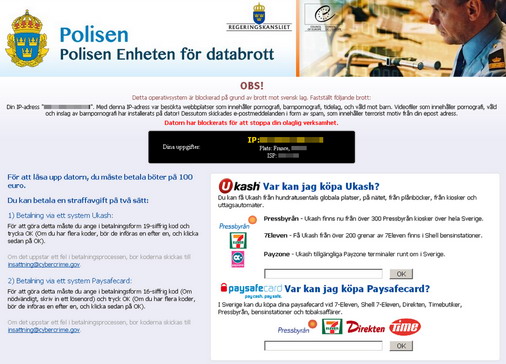
A couple of days ago I was summoned as “the computer guy” to look at a potential virus problem. It seemed that when logging on to the computer, a big message showed up claiming the police has blocked the computer. It also showed the computer’s ip and isp (all of which can easily be picked up by any program running on the computer). The message above says Detta operativsystem är blockerad på grund av brott mot svensk lag. Fastställt följade brott:. The message itself looks quite legitimate aside from some spelling problems, so i can see how some might get scared by this.
The nasty part of the message is that after it showed up the computer wouldn’t respond to most commands like Alt+Tab, Alt+F4 etc. Ctrl+Delete worked however, but the task manager could not be started. Only option was to log out again (through Ctrl+Alt+Delete prompt). Other accounts on the same computer however did not show the same signs of infection, so I could do some research (using google) on another account. I tried running a full scan on the computer from another account, but nothing interesting showed up. After a few other dead ends I found a solution that worked, so maybe this can help someone else too.
Prerequisites:
Alternative 1:
- Usb stick (about 1Gb should be enough)
- UNetbootin : This is a small application that can burn images onto a usb memory stick, which can then be used to boot the computer from the memory stick. Download application here. Remember where you save it (an exe file), it does not come with an installer.
Alternative 2:
- Empty CDROM
- CD Burner application (that can burn iso files)
- Kaspersky Rescue Disc : This is a linux distro that comes with kapersky applications already installed and that can be booted from CD or usb memory. Download iso file here
Removal
- Alt 1: Install iso onto usb drive, Alt 2: Burn iso onto an empty CDROM
- Boot with usb drive into Kaspersky Rescue OS
- Run Kapersky windows unlocker, for more detailed instructions follow the link under resources.
- Start a terminal
- Run the command windowsunlocker
- Run command 1 to clean the registry (note any file paths to suspicious files).
- Run command 2 to save boot sector copies
- Optional: Run a full scan
- Startup the computer, now the message should not show up anymore
- Remove the suspicious files manually, i found two files located at:
C:\Users\<Username>\AppData\Roaming\deo0_sar.exeandC:\Users\<Username>\AppData\Loacal\Temp\deo0_sar.exe